Phishing is a type of online scam, typically sent via email. The purpose is to gain access to sensitive information or money. The scammers do this by pretending to be a legitimate sender. For example, your boss, your bank, the post office or someone close to you.
Phishing has been around for a long time and the most famous example is probably the 'Nigerian prince' of the 1990s. Since then, this form of fraud has become increasingly sophisticated, which can make it quite tricky to identify a phishing attack. The typical phishing email asks for personal details, a payment or includes a link/file with malware.
Phishing examples:
- The sender pretends to be a logistics company (like DHL or UPS). The message states that they are unable to deliver your parcel and asks you to update your delivery details by clicking on a link.
- The sender claims to be your bank and asks you to urgently update your login details.
- The sender claims to be Paypal and states that you need to update your credit card details.

Phishing is a type of fraud that involves gaining access to sensitive information or money.
Read about 5 phishing mistakes all organizations do and how to prevent them.
Different types of phishing
Phishing comes in different forms. That is why we have created this handy list for you! Here you can learn all you need to know about phishing.
Read about some of the most common types of phishing scams and what they may look like below. In addition, we have provided you with some handy tips on how to recognize and protect yourself against a phishing attempt.
What is spear phishing?
Spear phishing is a form of phishing attack that targets one person, or a small group of people. The victim is typically a key stakeholder within a company, like someone in the finance department, the HR manager or an IT expert. To trick these people, the attacker pretends to be someone high up in a company, such as a CEO or the victim's direct manager.
Spear phishing vs phishing
The difference between spear phishing and traditional phishing lies in the number of recipients. Regular phishing emails are sent to a huge amount of people. The attackers simply throw out as many hooks as they can. Spear phishing is much more personal, and the victim is addressed by name.
It is also common that scammers target the CEO or the management within a company. This kind of spear phishing is called whaling.
Spear phishing examples:
- The attacker pretends to be the company's CEO and asks a person in the finance department to transfer a large sum of money. This is urgent and much is at stake if it is not done within a short amount of time.
- The attacker is impersonating a CISO and manages to trick someone in the IT-department to give out their login to important systems.
- The attacker pretends to be part of the IT department and asks you to click on a link to upgrade your software. In reality the link includes malware.

Spear phishing targets one person or a small group of people.
What is smishing?
Smishing is short for SMS phishing. Just as it sounds, it is a form of phishing sent via text messages. The aim is to gain access to your personal data or to get money. As we initially stated, phishing attacks are typically being sent by email. But other forms like text messages and phone calls are becoming more common. (More on telephone phishing later).
Just as in traditional phishing, the attacker pretends to be a trusted sender such as your bank, your boss, the tax authorities and so on.
Common examples of smishing messages:
- Suspicious activity or login attempts have been detected on your account.
- There is a problem with your account or payment information.
- You need to confirm personal information.
- You need to click on a link to make a payment.
- You have received a discount code or coupon. Click here to claim it.
- You have won a prize and you need to claim it.
What is vishing?
Vishing is when scammers call you and try to get personal information over the phone. This could be your account number, password or personal information.
Vishing stands for voice phishing. This type of attack can be difficult to recognize as it is hard to verify the identity of the person you are talking to. If someone says they are calling from the bank, your first thought might not be that they are lying to you.
Vishing examples:
- The attacker states that they are calling from your bank to inform you that there is a problem with your account or credit card.
- The attacker states that they are calling from a government agency and ask you to confirm personal details.
- The attacker states that they are calling from the customer service department of a well-known company and need your details to sort out an invoice.

Vishing attacks can be difficult to catch as it’s hard to confirm the identity of the person you are talking to.
Why is phishing effective?
Most people can identify a traditional phishing attempt. Not clicking on unknown links is basically the first thing you learn about cyber security. Well, that and to not use the same password for every account you own.
What makes phishing and smishing so successful is the quantity being sent out. If over 1000 phishing messages are sent out in a day, it only takes a fraction of them to be successful for it to be profitable for the attackers to continue.
Instead, spear phishing and vishing rely on the credibility of the people the scammers are impersonating. The victim is more likely to do what they are told because they think they are talking to someone they know or a brand they trust.
Read about which companies and organizations that are extra vulnerable to phishing attacks.
How to prevent phishing attacks
The first step is to be aware of the risks and know how to recognize a phishing message or call.
Always be critical when someone asks you to make a payment or give out personal information. Using secure email software, such as Smartlockr, will also make you extra alert to phishing messages. By notifying you when you send an email outside of your organization, and by allowing you to confirm recipients and files, you are more aware when receiving suspicious messages.
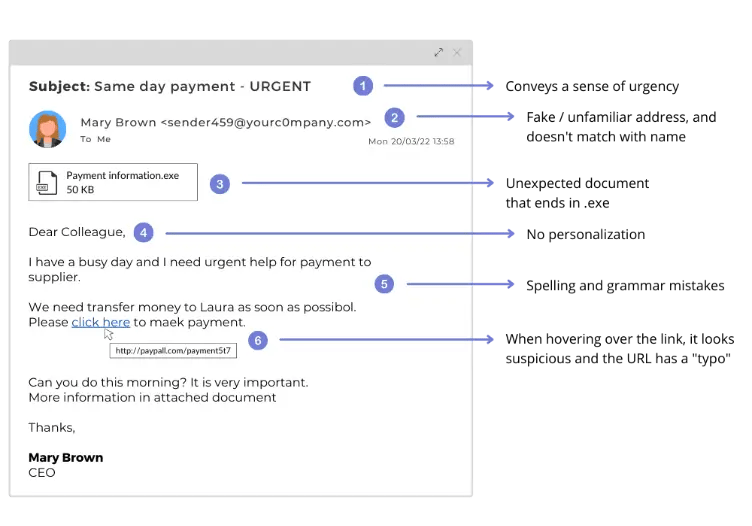
How to identify phishing emails
There are some handy tricks to recognize a phishing email. Check out our list of what to be aware of below:
- The email address does not match the sender. For example, you have received a message from DHL but the email address is 'dfg123@gmail.com'.
- You are asked to do something urgently.
- You are asked to provide personal or sensitive information or to make a payment.
- The message contains many spelling and grammatical errors.
- The domain name is not correct or does not appear to be official (extra numbers or letters are added). For example, you have received an e-mail from customerservice@paypal1.com
- Beware of clicking on links and attachments. By hovering with your mouse over a link (without clicking it) you can display where it leads. Does it look suspicious? Send it to your CISO!
Are you curious to learn more about sending secure email? Download our e-book below.